Identity for
autonomous agents
Use the x402 paywall model to ensure agents must present a valid ZK credential before performing high-impact or compliance-sensitive actions.
Use the x402 paywall model to ensure agents must present a valid ZK credential before performing high-impact or compliance-sensitive actions.
End users
Agents acting on your behalf should not expose your identity. Today, they do. Every API call, every form submission, every transaction leaks metadata.
Service companies
You're responsible for preventing malicious or non-compliant agent behaviour, but you can't verify their identity or intent. Heavy KYC requirements don't make sense in the agentic AI world.
Regulators
Static KYC doesn't apply to autonomous systems. You need dynamic, real-time visibility into whether an agent is legitimate without gaining access to the underlying identity or sensitive data.
Infrastructure
Autonomous agents create new load, new surfaces, and new risks for the platforms that host them. You're expected to provide reliability, throughput, and safe execution.
Use the x402 paywall model to ensure agents must present a valid ZK credential before performing high-impact or compliance-sensitive actions.

A privacy-preserving way for an agent to prove it is not acting on behalf of a banned, sanctioned, or malicious entity.
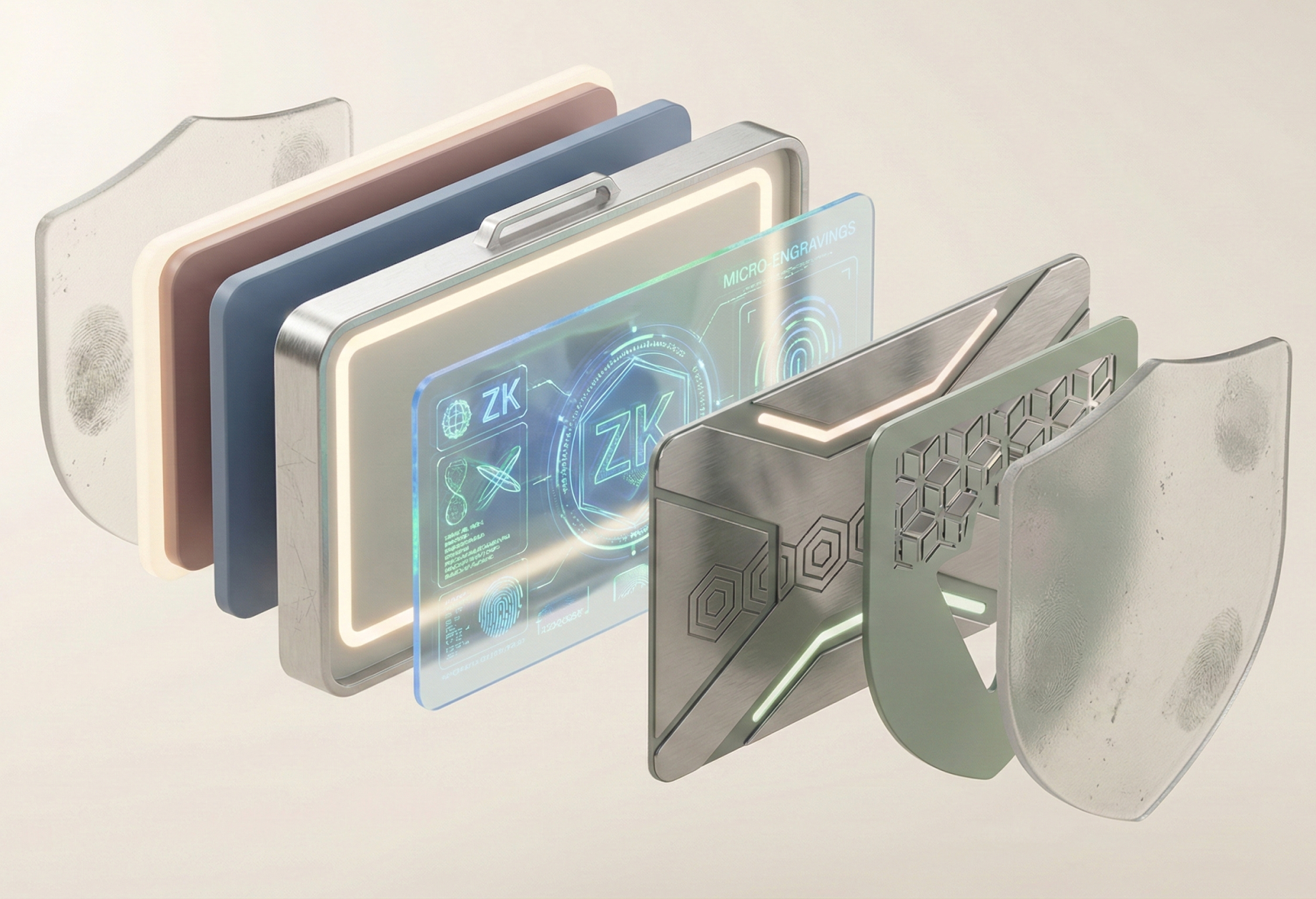
Agents generate one ZK credential and reuse it across wallets, apps, or smart-contract systems without repeating verification or leaking identity.

Why This Matters for the x402 Agent Ecosystem.
x402 is creating an ecosystem where autonomous agents can act on behalf of users, wallets, and services. What's missing is a trusted, privacy-preserving identity and compliance layer that keeps the system safe without exposing personal data.
How it works
The user creates a private, zero-knowledge credential.
A credential is generated on the user's device using their verified identity, but the underlying data never leaves the user's control. Nothing is uploaded, stored, or exposed. What exists is a mathematical proof that can answer very specific questions — without revealing anything else.
zkSELF validates the proof through the x402 gateway.
The proof is sent through the 402 flow and checked against the zkSELF verifier stack. The system confirms that the user meets the requirement — age, residency, KYC status, whatever the service needs — and does so without ever revealing who the user is.
The service receives a simple, unambiguous "allowed / not allowed" signal.
Instead of handling sensitive identity documents, the service receives a binary eligibility flag and nothing more. Full compliance. Zero PII footprint. Instant access for the user; minimal liability for the service.
Frequently Asked Questions
Find answers to common questions about our product and services.
Zero-knowledge proofs are more mature, have better tooling, and are specifically designed for proving statements without revealing data. FHE is powerful but adds computational overhead that isn't necessary for identity verification use cases.
Hardware-based solutions like SGX require trust in the hardware manufacturer and have known vulnerabilities. ZK proofs are mathematically verifiable and don't depend on trusting any specific hardware or vendor.
The underlying identity data never leaves the user's device. Only mathematical proofs are transmitted, and these proofs reveal nothing about the actual data — they only confirm specific claims.
No. It replaces exposure to sensitive identity information while preserving the ability to enforce compliance. Users still complete KYC once, but services only receive a yes/no eligibility signal.
This is what the future looks like.
Do you want to discover these technologies? See the opportunity for integration in your IT systems.